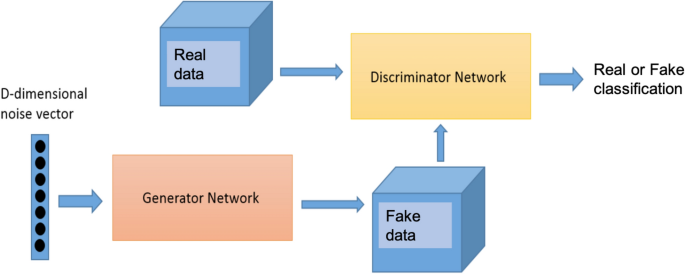
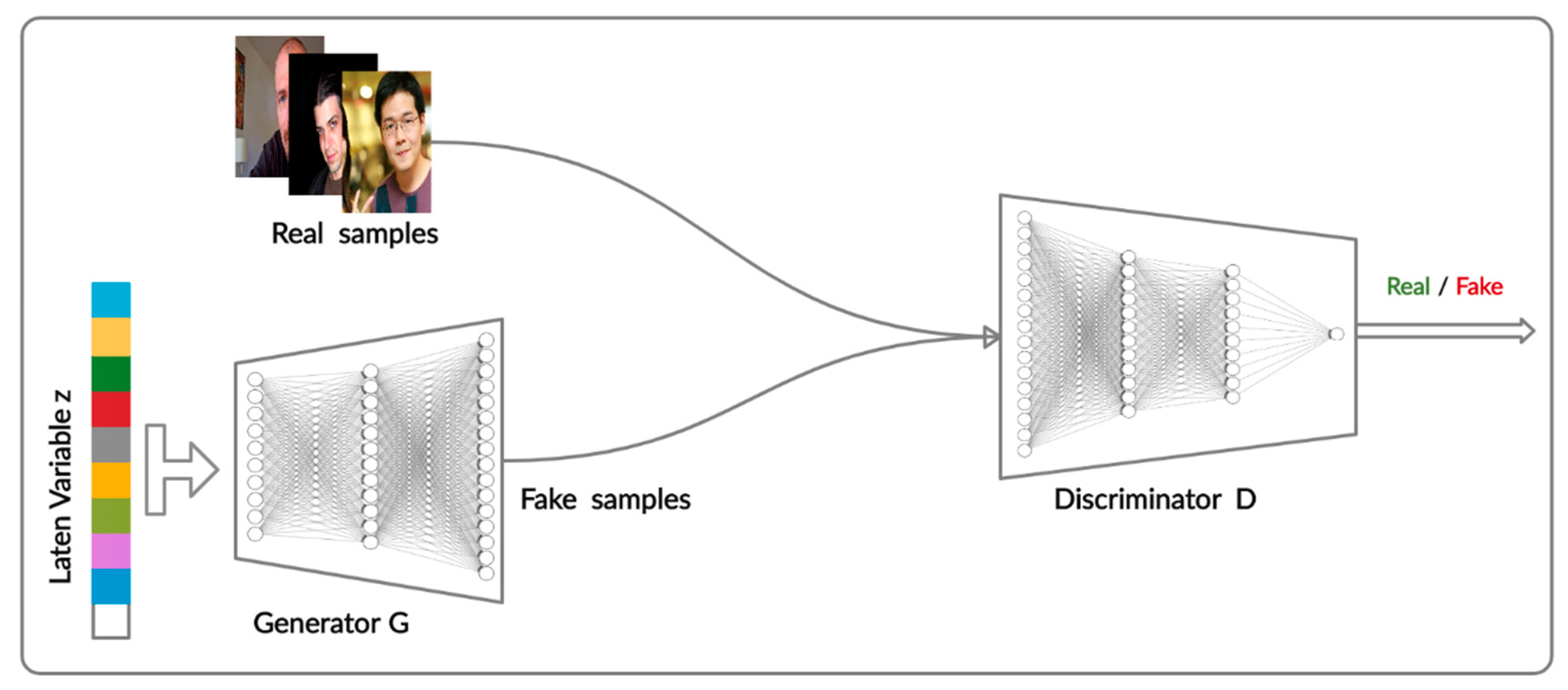
Synthetic flow-based cryptomining attack generation through Generative Adversarial Networks | Scientific Reports
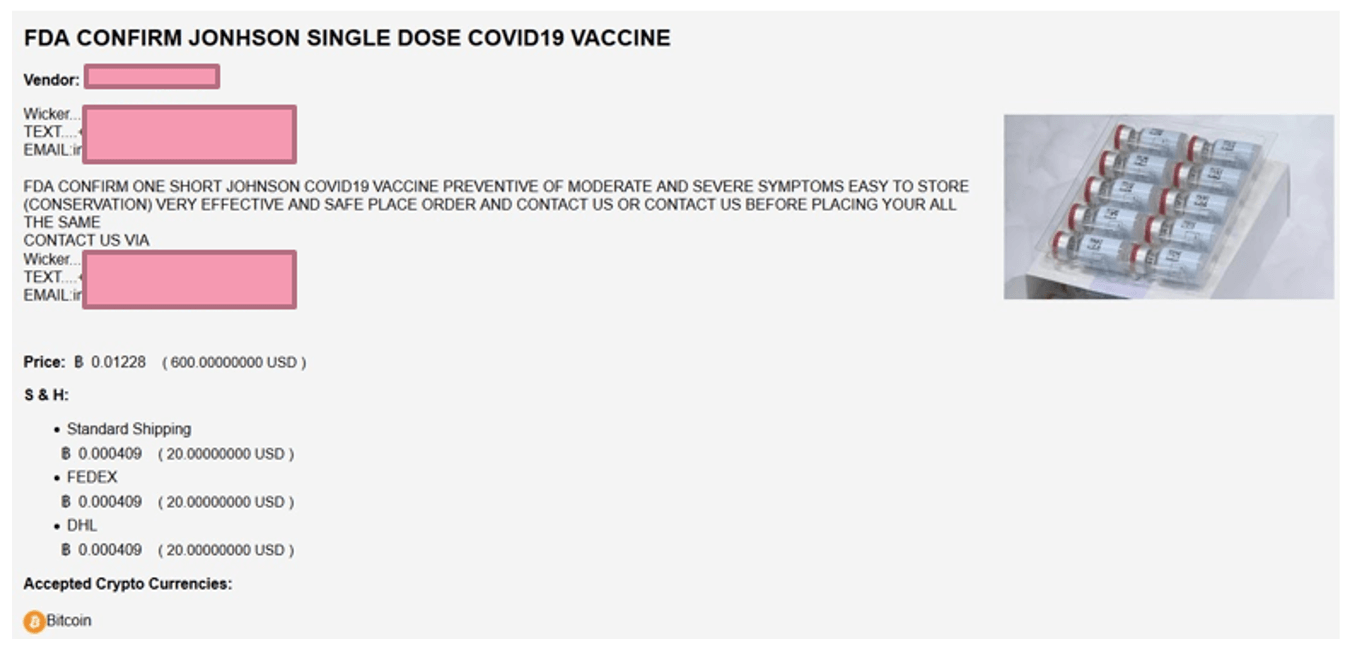
A passport to freedom? Fake COVID-19 test results and vaccination certificates offered on Darknet and hacking forums - Check Point Software






![Fake Address Generator [Name, City, Address, Credit Card] | SEOToolsCentre Fake Address Generator [Name, City, Address, Credit Card] | SEOToolsCentre](https://seotoolscentre.com/uploads/how-to-generate-fake-address-online-step-5.jpg)